>> mrt 2018: -5- keys en filezilla
keyd logon by filezilla
- create a virtual linux mint 18 clone
- create my two users (example: bob and dylan) in mint18-clone
bert@mint18-M02 ~ $ sudo useradd -m bob [sudo] password for bert: bert@mint18-M02 ~ $ sudo useradd -m dylancheck the work
bert@mint18-M02 ~ $ tail -n 2 /etc/passwd bob:x:1001:1001::/home/bob: dylan:x:1003:1003::/home/dylan:create passwords:
bert@mint18-M02 ~ $ sudo passwd bob Enter new UNIX password: Retype new UNIX password: passwd: password updated successfully bert@mint18-M02 ~ $ sudo passwd dylan Enter new UNIX password: Retype new UNIX password: passwd: password updated successfully - give access to centOS by password
[bert@cOS74-T06-2 ~]$ sudo passwd bob [sudo] password for bert: Changing password for user bob. New password: Retype new password: passwd: all authentication tokens updated successfully. [bert@cOS74-T06-2 ~]$ sudo passwd dylan Changing password for user dylan. New password: Retype new password: passwd: all authentication tokens updated successfully. - bob & dylan generate keys and put them on centos
bert@mint18-M02 ~ $ sudo su bob bob@mint18-M02 /home/bert $ cd bob@mint18-M02 ~ $ ssh-keygen Generating public/private rsa key pair. Enter file in which to save the key (/home/bob/.ssh/id_rsa): Created directory '/home/bob/.ssh'. Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/bob/.ssh/id_rsa. Your public key has been saved in /home/bob/.ssh/id_rsa.pub. The key fingerprint is: SHA256:M2dDQcKXrIVWuD7Oc0AoqWgM1RjhTRImNolqx1H0mmc bob@mint18-M02 The key's randomart image is: +---[RSA 2048]----+ |ooB*+o ..*+. | |o=+=. . =.=. | |..o o. + =. | |o. oo + +. | |+... + ES + | |.o. o += . | |. o o | | + . | | o | +----[SHA256]-----+ - put the key on centOS
bob@mint18-M02 ~ $ ssh-copy-id 10.104.198.106 /usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "/home/bob/.ssh/id_rsa.pub" The authenticity of host '10.104.198.106 (10.104.198.106)' can't be established. ECDSA key fingerprint is SHA256:OFUuD0gVNHojUseVGgrDfq6F4nzPNokpZ2p98aUbzBg. Are you sure you want to continue connecting (yes/no)? yes /usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed /usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys bob@10.104.198.106's password: Number of key(s) added: 1 Now try logging into the machine, with: "ssh '10.104.198.106'" and check to make sure that only the key(s) you wanted were added. - check whether keys are needed to logon
bob@mint18-M02 ~ $ ssh 10.104.198.106 bob@10.104.198.106's password: Last login: Fri Mar 16 11:42:31 2018 [bob@cOS74-T06-2 ~]$ exit logoutthe machine is playing with our brain ...
since this worked for the sysadmin user, there is a problem with the position of the home directory ... and then we think about SElinux ...
- solution
To cut a long story short we have to givesshon centOS access to/www-homes/.ssh
this worked ....[student@cOS74-T06-2 ~]$ sudo semanage fcontext --add --type ssh_home_t "/www-homes/.*/\.ssh(/.*)?" [student@cOS74-T06-2 ~]$ sudo restorecon -Rv /www-homes - convert private key to filezilla ppk format
- install filezilla and putty-tools on bob's linux mint machine (bob and dylan share one machine for testing)
- convert bob's private key into a ppk key for filezilla:
cd $HOME/.ssh puttygen .ssh/id_rsa -o bobs-privates.ppk
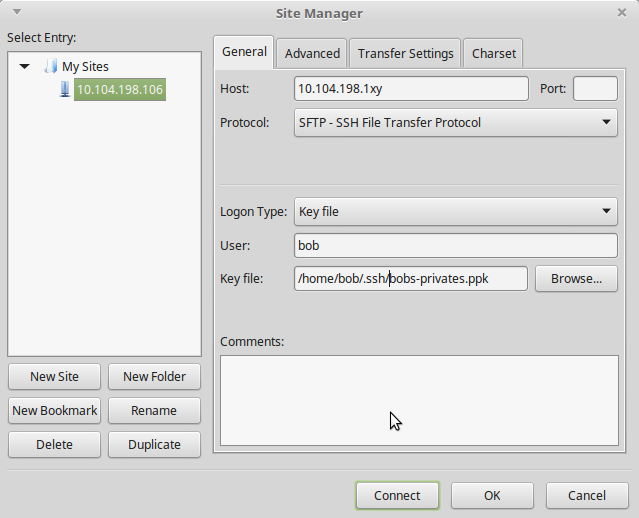
- configure filezilla
- disable password for bob and dylan
[student@cOS74-T06-2 ~]$ sudo passwd -l bob
- problem: user bob sees the entire filesystem
this was not asked in the assignment, so this is not obligatory ...
we have to chroot the sftp users as explained in
http://linux800.be/services/services-adv-2/oef-sftp-ub16-04/sshd-config